Like compute and storage, networking is also an essential part of the cloud. Networking is very broad topic and many network security components also come under this. In cloud, Networking components have been distributed into multiple small components and architecture has become distributed architecture. However, this distributed architecture methodology exists across cloud landscape.
I always suggest having an architecture start from Networking because your network define your boundaries. However, people can have debate that with cloud we are open and we can’t define boundaries. I totally agree with you as you are thinking from end-user’s perspective. In my view, if you can’t define the boundaries then you can’t have appropriate security in place. If you are working with multiple SaaS/PaaS/IaaS vendor, that’s fine but define them in your enterprise architecture so that what, how, where and when, you are sending your data is captured. This debate can’t happen through blogpost, therefore let me explain you key networking components in Azure and their mapping with on-premises networking stuffs.
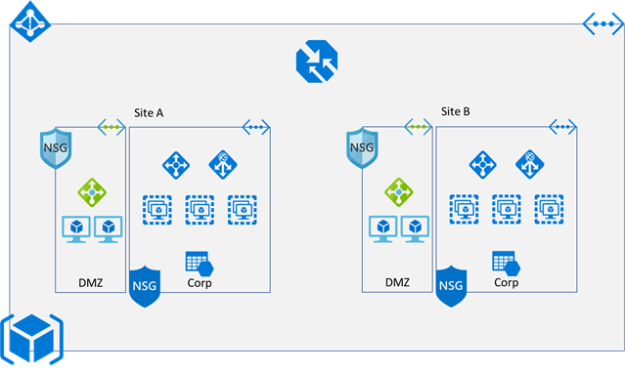
Once you try to map the networking components of your on-premises with cloud, you observer that most of the things are available but it has slightly different name or functionality.
LAN ßà Virtual Networks
VLAN ßàAddress Space and Subnet
Lag between switches ßà VNet Peering / VNet-to-VNet connectivity
WAN ßà Global VNet Peering / VNet-to-VNet connectivity
MPLS ßà Express Route
L4 load balancer ßà Load balancer
L7 load balancer ßà Application Gateway
Geo-DNS/Global load balancer ßà Traffic Manager
Firewall ßà Network security group / Network virtual appliance
To know about major component and its functionality, read the following blogposts:
Once you know the boundaries, big picture and bottlenecks, and understand the Azure capabilities as well then you will design a best possible solution.